No one likes a know-it-all, but we’re not here to make friends. We’re here to make organisations resilient. To make sure they’re prepared for what’s coming, and to make sure they can recover quickly when they need to.
So, that’s why we don’t mind saying it:
We told you so.
As long ago as 2020, we were telling businesses that they needed to be ready for a data breach. That cyber security alone wasn’t enough. That a breach was inevitable. That they needed to shift from a defensive strategy to a resilience one.
More specifically, we’ve been telling them they need to prove they can recover their critical systems before they find themselves trying to do it for the first time in the middle of a crisis.
And, of course, it’s not only us that has been saying it. This is a point of view shared by many industry experts and analysts.
The big question is: Has anyone been listening?
While lots of organisations have taken notice — which is evident from the increasing number of them subscribing to Predatar’s Recovery Assurance platform — the reality is that far too many have chosen to keep their heads in the sand.
Until now.
What’s changed?
It’s not entirely true that Claude Mythos, the latest AI model from Anthropic, hasn’t changed anything. It is shining a huge and unignorable spotlight on the inevitability of data breaches. If you’re not familiar with Mythos, or its alarming potential in the wrong hands, you can learn more here.
Mythos is being discussed in almost every boardroom around the world. If you work in an IT, business continuity, operational resilience, or cyber security department, get ready for some tricky questions coming your way soon. Questions like:
What does Mythos mean for our business?
What are we doing about it?
Are we ready for a breach?
… but do you have the answers?
Patch faster?
The clearest recommendation from Anthropic is: patch faster, and treat CVE-related dependency updates as urgent – highlighting how Mythos-class models can be used defensively to identify and remediate vulnerabilities before hackers do.
If software manufacturers and IT teams continue to use current approaches for patch creation and deployment, they simply won’t keep up with the speed of the AI-powered vulnerability exploits that are coming down the tracks. That’s why the concept of patching at machine-speed is gathering popularity – an approach where AI and automation are deployed to dramatically close the patching window.
While this type of defensive approach will soon be essential, it’s a bit like AI-powered whack-a-mole. If faster patching is your only answer to the Mythos questions, you’re in trouble.
The unavoidable truth
Organisations simply can’t hide from the facts anymore. It isn’t possible to defend against every threat. The ability to execute a rapid, rock-solid recovery is essential.
Don’t be misled by Service Level Agreements (SLAs), untested Recovery Time Objectives (RTOs), or recovery guarantees from your suppliers and technology vendors. The only way to be certain that you can execute a fast, clean, successful recovery is to test it – to actually recover your critical systems and check that they are safe…
Not once a year.
Not once a month.
Every day!
Recovery Assurance with Predatar
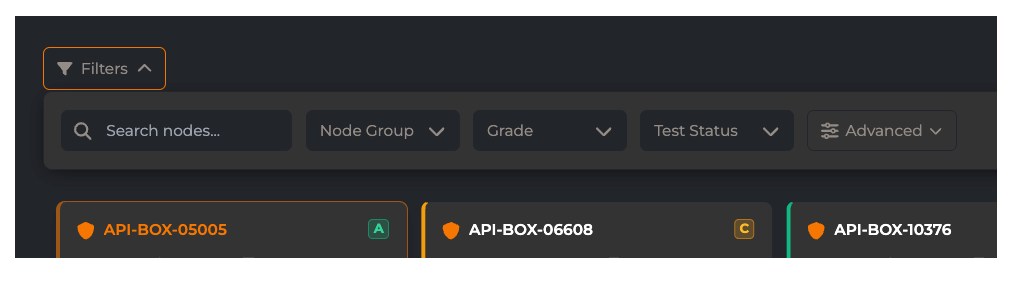
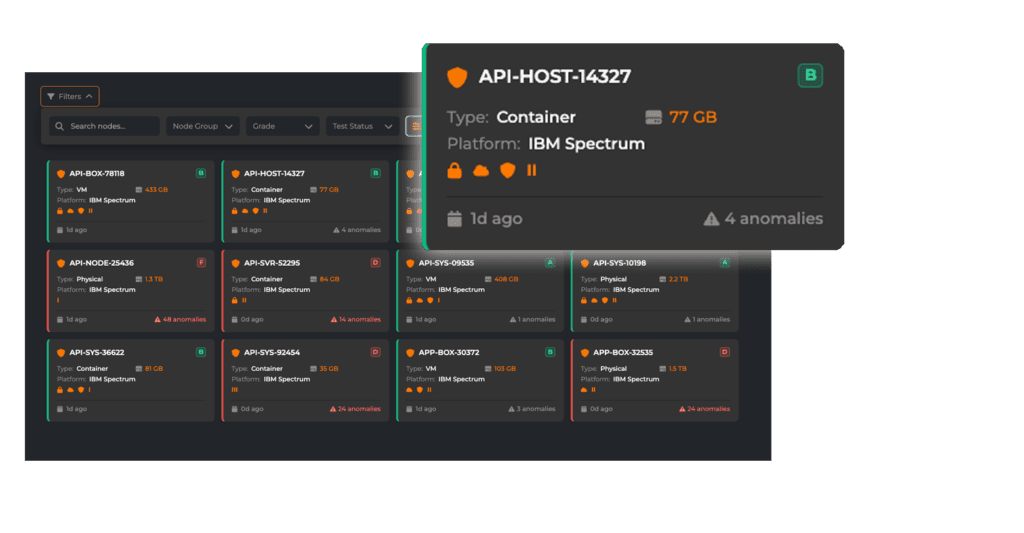
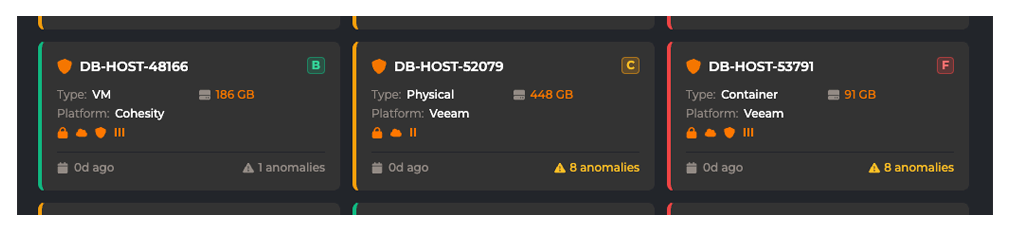
Predatar’s Recovery Assurance platform puts AI and automation to work to continually validate that the critical systems your business relies on can be recovered quickly, cleanly, and completely — even if the data they are built on lives across fragmented, multi-vendor storage and backup infrastructure.
Not only is this proactive approach a good idea, it also provides the evidence of resilience that helps board-level executives sleep at night. So, when those big questions come down from the top – answer them with proof of resilience.
Start your journey to proven resilience
Talk to a Recovery Assurance expert or book a Predatar demo.